In today's digital age, cyber security is essential in nearly all aspects of life. People spend much of their lives online: they do their banking, access government services, work, store pictures and videos, connect with family and friends, and purchase goods. It’s no secret that the internet has brought a significant amount of opportunities, but it has also produced new threats that can compromise our privacy and security.
Cyber security breaches can have critical consequences for organizations, including identity theft, financial losses, data theft, damage to national security, reputational damage, and legal liability, to name only a few. It is up to organizations to ensure their employees are equipped with the knowledge and skills to identify and mitigate these threats. With the right knowledge and habits, public servants can become a crucial line of defence against cyber attacks.
Over the last two years, cyber security has become a top concern for Canadians. Ransomware incidents hit the headlines on an almost daily basis both in Canada and around the world. Our essential services are being disrupted, from hospitals and schools to municipalities and utility providers. Our personal and financial data are being stolen, traded, or leaked online. – The Honourable Anita Anand, Minister of National Defence
Why is cyber security knowledge and readiness important?

Organizations can protect themselves through IT security, encryption of networks, virtual private networks, by securing devices and training employees. However, even the most robust security systems are vulnerable to human error. In fact, according to the Verizon Data Breach report, in 2022, 82% of breaches involved human error.
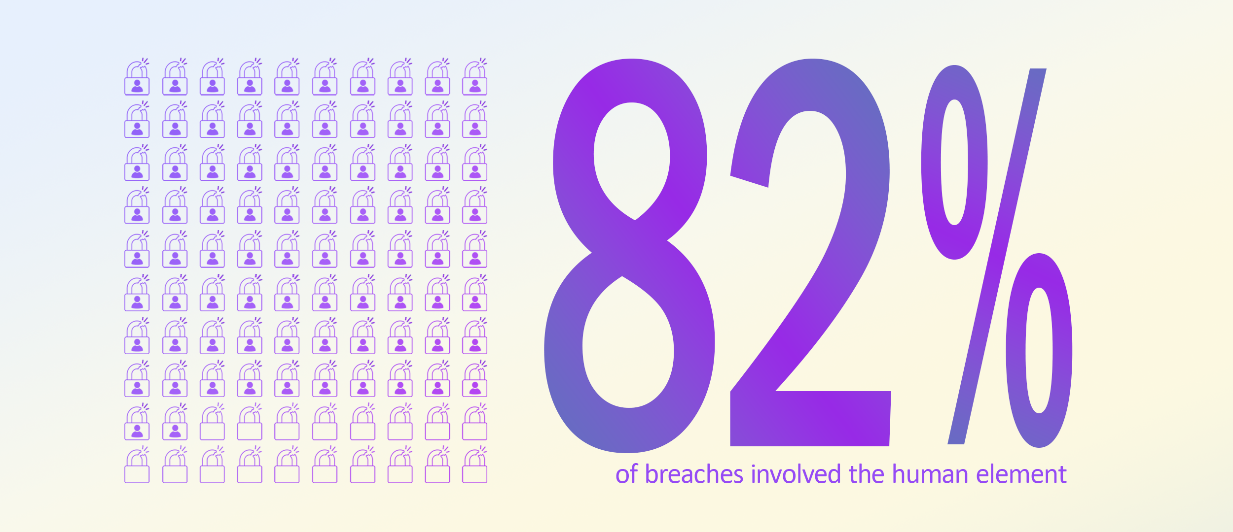
Despite the increasing sophistication of cyber attacks, it’s often humans mistake that leaves an organization vulnerable. Common examples of human error include weak passwords, falling for phishing scams, and the unintentional disclosure of sensitive information. In some cases, employees may even unwittingly download malware or other harmful software onto their computers, generating a backdoor for hackers to explore. Cyber security concerns everyone.
Four reasons why cyber security knowledge is foundational to all employees
Definition of terms
Malware: Malicious software designed to infiltrate or damage a computer system, without the owner's consent. Common forms of malware include computer viruses, worms, Trojans, spyware, and adware.
Phishing: An attempt by a third party to solicit confidential information from an individual, group, or organization by mimicking or spoofing a specific, usually well-known brand, usually for financial gain. Phishers attempt to trick users into disclosing personal data, such as credit card numbers, online banking credentials, and other sensitive information, which they may then use to commit fraudulent acts.
Ransomware: A type of malware that denies a user's access to a system or data until a sum of money is paid.
Social engineering: The practice of obtaining confidential information by manipulation of legitimate users. A social engineer will commonly use the telephone or internet to trick people into revealing sensitive information. For example, phishing is a type of social engineering.
Distributed denial-of-service (DDoS): An attack in which multiple compromised systems are used to attack a single target. The flood of incoming messages to the target system forces it to shut down and denies service to legitimate users.
Zero-day exploits: A zero-day vulnerability is a software vulnerability that is not yet known by the vendor, and therefore has not been mitigated. A zero-day exploit is an attack directed at a zero-day vulnerability.
- Protect sensitive data, Canada, and its people: Organizations have access to sensitive data, such as people’s personal information (for example, their date of birth, financial data, address, phone number, and email address) as well as sensitive government information. Strong cyber security habits help employees know how to safeguard data through their informed behaviour, thereby decreasing the risks of data breaches. It will allow employees to understand and recognize the various risks associated with handling data. Additionally, it can help safeguard critical infrastructure, such as energy grids, transportation systems, and the healthcare system, which are essential to the well-being and security of people in Canada.
- Reduce the risk of cyber attacks: With cyber actors becoming more effective and hackers constantly seeking new vulnerabilities, cyber security skills are vital to protect Canada's government and its people. Providing cyber security training will help staff protect the organization’s security infrastructure from threats, recognize possible vulnerabilities (or risks), and take measures to prevent cyber attacks. To ensure it is a comprehensive learning process, it should include education on malware, phishing scams, ransomware, social engineering, distributed denial-of-service (DDoS), and zero-day exploits. When an employee learns how to identify the tactics used by hackers to infiltrate networks and knows to report them, it means that systems are less likely of being attacked and that people in Canada are less likely to be victims of malicious activity.
- Build a culture of security awareness: Cyber security is everyone’s responsibility, not just the IT department. Broad awareness of cyber threats and the skills to prevent them will actively support changing mindsets and behaviours and will instill a common culture of security. Employees will be aware of existing risks and will be proactive about identifying and reporting potential threats. They will take the necessary measures to protect and defend themselves, their teammates, and the organization from cyber attacks.
- People will keep making the same mistakes if they don’t know what they don’t know: Without solid cyber security foundations, employees will keep making the same mistakes, (for example, clicking on nefarious links) because they are unaware of the security consequences. This can threaten the confidentiality, integrity, and availability of the organization’s assets. Employers need to help employees recognize the signs of a cyber attack, such as phishing scams and social engineering tactics, and empower them to take proactive steps to prevent a breach.
Having a whole-of-organization approach to cyber security practices and informed technology habits decreases the risks to network security, data protection, and the continuity of operations and services. It also ensures everyone, everywhere is on the same page and has a basic level of proficiency on the subject. The need for knowledge in cyber security will only continue to increase.
You can take steps to learn how to protect yourself online and protect sensitive information. Start by taking some of the following courses.
- Course | Discover Cyber Security (DDN235)
- Course | Cyber Security in the GC and Online Exposure (DDN233)
- Course | Privacy in the Government of Canada (COR504)
- Course | Access to Information and Privacy Fundamentals (COR502)
Autres ressources
- Évaluation des cybermenaces nationales 2023-2024
- Centre canadien pour la cybersécurité
- Signaler un cyberincident (pour les individus et les organisations)
- Pensez cybersécurité